Build Secure Network Infrastructure without Compromising Production Efficiency
While companies are tapping into the opportunities that the Industrial Internet of Things (IIoT) has to offer, digitalisation has become a key initiative for industries. Digitalisation has allowed the industrial control system (ICS) landscape to develop quickly in recent years.
Originally, ICS networks were physically isolated and almost immune to cyber attacks. However, recently, there has been a rise in the sophistication of cyber attacks, which has prompted everyone from IT to OT personnel to produce solutions that enhance industrial cybersecurity. Thus, understanding industrial cybersecurity requirements will help companies mitigate cybersecurity risks.
Debunk Industrial Cybersecurity Myths
There are some myths about industrial cybersecurity that may put your facilities and businesses at risk. Watch the video to learn how to debunk the myths and build defense-in-depth security for your industrial networks to ensure continuous operations and the safety of personnel.
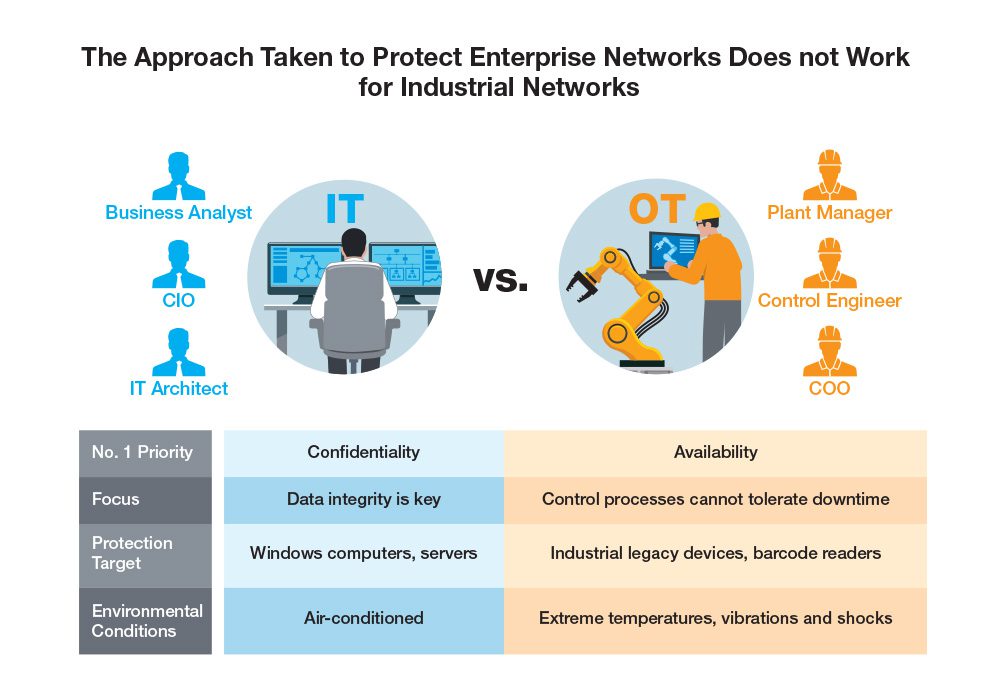
Vast Differences Between IT and OT
Case Studies
With over 30 years of experience in industrial networking, Moxa draws on this expertise to help customers build secure networks by offering protection for PLCs, SCADA systems, factory networks, and remote access. Download the case studies to learn more.

Customer: CNC Machine Builder
Challenges
Maximising network uptime enhances machine productivity. Therefore, a leading manufacturer of mechanical power presses needed to provide a timelier and more efficient after-sales service in order to ensure improved machine performance and effective troubleshooting.
At first, the machine builder adopted Windows-based Remote Desktop Control (RDC) technology, but security risks and additional costs came at a high price. Furthermore, the Windows-based computer by itself is susceptible to security risks, and the possibility of attacks increases even more when the computer connects to the Internet

Customer: Automotive Parts Plant
Challenges
An automotive parts plant manager planned to digitalise their production processes. The field devices run on the EtherNet/IP protocol for control unification and data acquisition. As the network infrastructure in this plant is on a large scale, it is very difficult for the plant manager to monitor all devices and visualise the network topologies.
In addition, to realise digitisation, all networks are interconnected from the field site all the way to the ERP and even to the cloud. It is essential to have good cybersecurity measures to allow this transformation to occur, without compromising production efficiency.

Customer: CNC Machine Builder
Challenges
Maximising network uptime enhances machine productivity. Therefore, a leading manufacturer of mechanical power presses needed to provide a timelier and more efficient after-sales service in order to ensure improved machine performance and effective troubleshooting.
At first, the machine builder adopted Windows-based Remote Desktop Control (RDC) technology, but security risks and additional costs came at a high price. Furthermore, the Windows-based computer by itself is susceptible to security risks, and the possibility of attacks increases even more when the computer connects to the Internet
Checklist for Your Industrial Cybersecurity
You can use the checklist below to make sure you do not forgot any of the defense-in-depth security measures and select solutions that fit your needs. Download the checklist and recommendations.

- Identify And Control Who Can Log In The Devices
- Increase Password Complexity To Enhance Access Control
- Verify Authorized Devices Before The Devices Gain Access To The Network And Communicate With Other Devices
- Encrypt Confidential Serial Interfaced Data To Ensure Data Integrity
- Encrypt Configuration Data To Increase Confidentiality
- Select Device Vendors That Respond Quickly To Reported Vulnerabilities And Fix Them

- Segment Large-Scale Networks Into Smaller Networks To Avoid Networking Issues Interrupting Operations Or Bringing The Entire Network To A Halt
- Filter Out Unauthorised Packets And Block Unauthorized Access To Enhance Access Control
- Create A Secure Tunnel For Encrypted Data Transmission To Ensure Data Integrity
- Deploy Industrial Firewalls, VLAN Or ACL, Which Are The Most Feasible And Cost-Effective Options For Industrial Control Systems

- Create Security Policies That Meet Your Network Requirements
- Ensure All Network Devices Are Configured To The Same Security Level
- Continuously Scan The Security Status Of Devices To Ensure The Whole Network Is Secure
- Regularly Monitor The Network To See If Any New Devices Were Added
- Save All Event Logs For Reference In The Event Of A Security Breach
- Compare The Network Configurations Before And After Incidents To Find The Root Cause Of The Problem
Choose the Solution That Works for You
Moxa offers a variety of connectivity and networking solutions to fulfill your different requirements. If you need to collect serial or Ethernet data, develop a security tunnel, or segment networks, we have the right solution to level up your connection security from every aspect.

If you need a solution that can securely send serial data into Ethernet networks
If you need a solution to protect data and networks from unwanted access during transmissions
If you need a solution to avoid entire network breakdown due to single product falling victim to a cyberattack





